Your data never leaves your infrastructure.
Every AI request is executed in your sovereign environment. Every response is encrypted. Every access is logged. No promises. Verifiable mechanisms.
What you risk with consumer AI
Most popular AI tools pose three risks that executives underestimate.

Three pillars, zero compromise
Sovereignty by default
Infrastructure is deployed in your country, in your isolated environment, or in a sovereign cloud. No data crosses a border. No third-party vendor has access to your requests or responses. Your data never leaves your isolated environment.
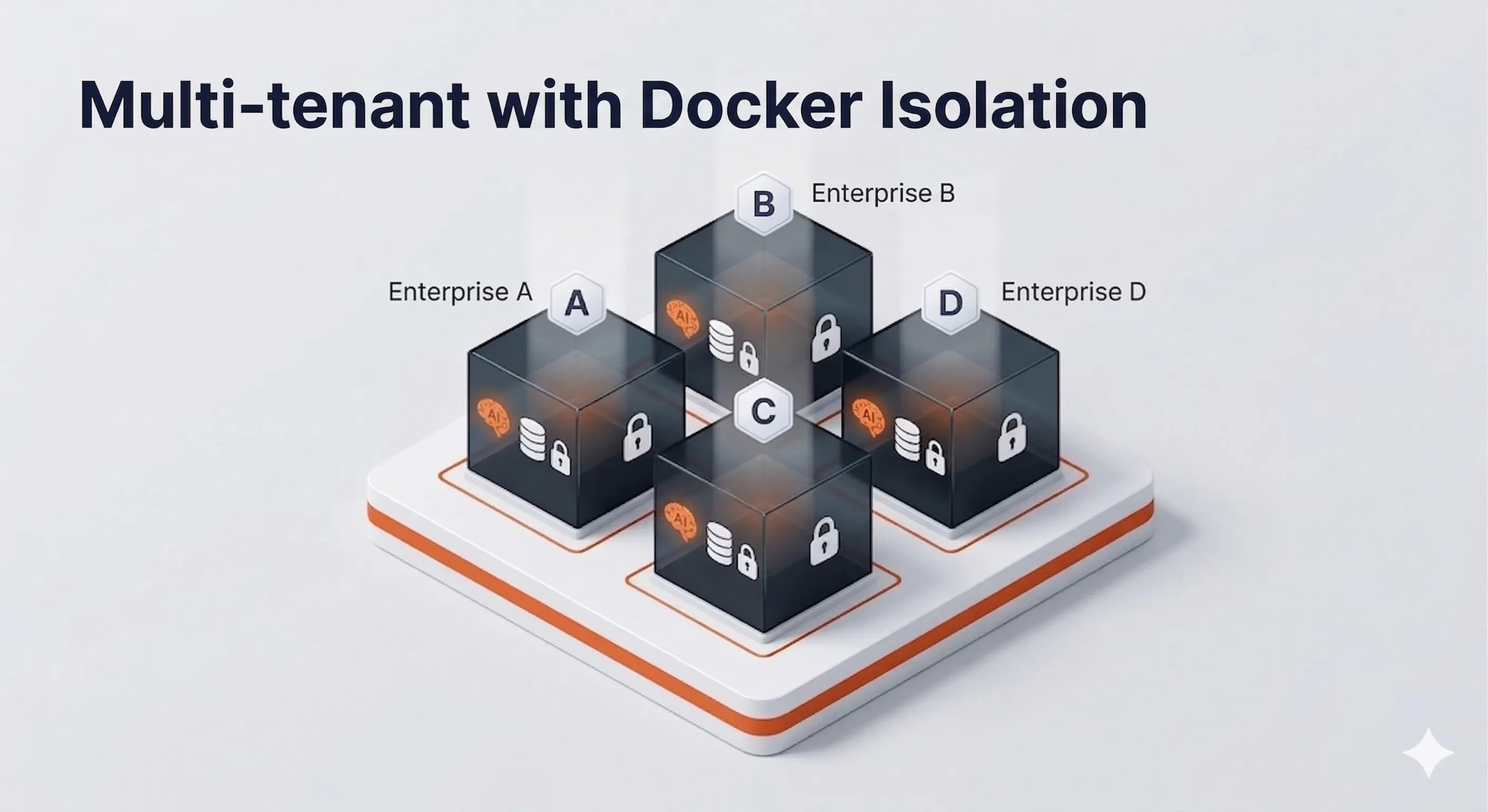
Isolation guaranteed by architecture
Each client has their own Docker container, their own database, and their own private network. Your data never comes into contact with another client's — you benefit from a dedicated environment.
Provable compliance
Every action is logged, timestamped, and exportable. In the event of a GDPR, CCPA audit, or internal review, you have a complete and actionable history. Not declarations. Evidence.
Every client in their own isolated environment
Unlike shared tools, your data never comes into contact with another client's data. Each SkaLean deployment creates a dedicated Docker container, a separate database, and an isolated network.
Dedicated Docker container
Your SkaLean instance runs in a fully isolated Docker container. No process, no memory, no network is shared with another client.
Separate database
Your data is stored in a PostgreSQL database that belongs to you. No shared tables, no common schema. Your data never coexists with another client's.
Isolated private network
Each environment operates on a private Docker network. Communications between your AI instance and your database never traverse a network shared with other clients.
8 layers of defense between your data and the AI engine
The AI engine never sees your real data
Before every request, SkaLean automatically detects 15 types of personal data in your text: names, emails, phone numbers, addresses, social insurance numbers, IBANs, dates of birth, and more.
This information is replaced by anonymous tokens before reaching the AI engine. The generated response uses the same tokens. SkaLean then restores the real values in the final response, visible only to the authorized user.
The AI engine never sees the actual data. The user sees no difference. The protection is invisible and requires no configuration.
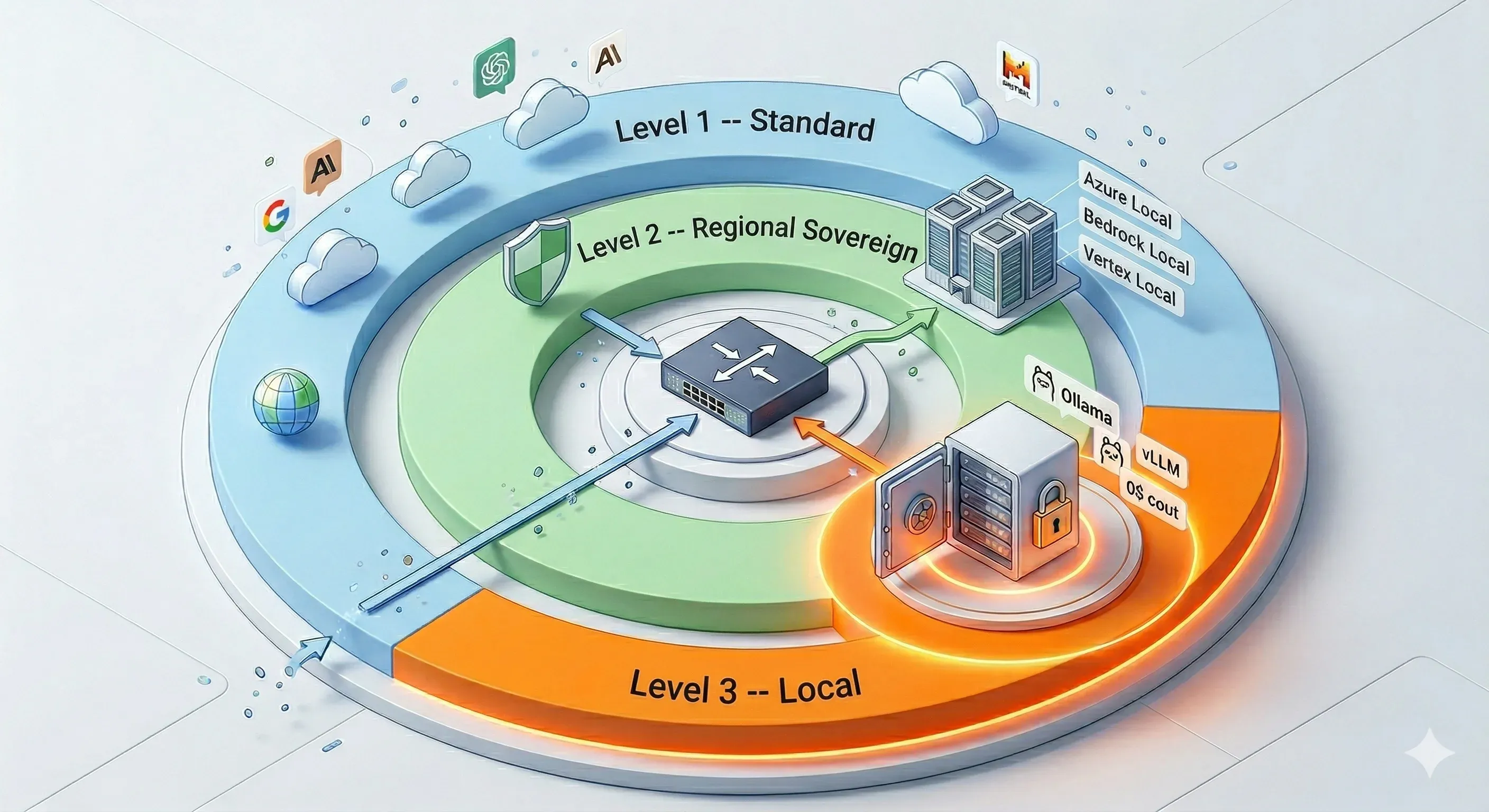
3 sovereignty levels — you choose
Depending on your industry and regulatory obligations, SkaLean adapts to the level of control you need.
Sovereign Canadian cloud
Your data stays in Canada on a certified infrastructure. Ideal for SMBs that want GDPR and CCPA compliance without server management.
- 100% Canadian hosting
- GDPR and CCPA native
- Maintenance included
- 99.9% uptime SLA
Regional private cloud
Dedicated infrastructure in your chosen cloud region (Canada, Europe, Asia-Pacific). Guaranteed physical isolation, no server neighbors.
- Dedicated servers for your organization
- Industry compliance (HIPAA, finance)
- Dedicated IP and private network
- Available in 12 regions
Self-hosted on your servers
SkaLean installs directly on your on-premise infrastructure. Zero data leaves your premises. Total control for the most demanding sectors.
- Data never leaves your premises
- Air-gap possible (closed network)
- Source code audit available
- Ideal for legal, healthcare, defense
The standards we uphold
GDPR, CCPA, HIPAA, OWASP — not as options, but as architectural foundations.
Top 10 Web Vulnerabilities
All protections from the OWASP Web 2021 framework are active on the platform.
- Protection against SQL, XSS and command injections
- Hardened access control and authentication
- Data encryption in transit and at rest
- Complete security event logging
Top 10 LLM Risks
Risks specific to language models are covered in accordance with the OWASP LLM 2023 framework.
- Prompt injection guardrails
- Automatic PII anonymization before LLM submission
- Model output isolation and validation
- Strict agency and permission control
Top 10 Agentic AI Risks
The architecture covers risks related to autonomous AI agents per the OWASP Agentic AI framework.
- Isolated sandbox per agent and per client
- Minimal and revocable permissions
- Audit of every action executed by the agent
- Configurable agency limits and guardrails
General Data Protection Regulation
Explicit consent, right to erasure, data portability, and processing registry natively integrated. Applicable in Canada and the EU.
- Automated right to erasure
- Exportable processing registry
- Granular consent by data type
- DPA (Data Processing Agreement) available
California Consumer Privacy Act
Right of access, deletion, and opt-out from the sale of personal data. Required for SMBs operating in the US or with California-based clients.
- Data sale opt-out
- Automatic inventory of collected data
- Response to requests within 45 days
- Certified access logs
Health Insurance Portability and Accountability Act
For clinics, medical offices, and healthcare companies. BAA (Business Associate Agreement) included on Tier 2 and Tier 3.
- PHI encryption at rest and in transit
- Access control by clinical role
- Immutable audit log for 6 years
- Signed BAA provided
SkaLean vs consumer AI
| Criteria | ChatGPT | Copilot | SkaLean |
|---|---|---|---|
| Data hosted locally | ✕ | ✕ | ✓ |
| Guaranteed multi-tenant isolation | ✕ | ✕ | ✓ |
| End-to-end encryption | ✕ | ~ | ✓ |
| Automatic PII masking | ✕ | ✕ | ✓ |
| Complete audit log | ✕ | ✕ | ✓ |
| 8 security layers | ✕ | ✕ | ✓ |
| HIPAA compliant (activatable) | ✕ | ✕ | ✓ |
| GDPR native compliance | ~ | ~ | ✓ |
Frequently Asked Questions
SkaLean follows a structured compliance and certification roadmap in 3 phases.
- Current phase (operational): GDPR, Quebec Law 25, HIPAA (activatable medical mode), OSFI (activatable financial mode). These compliances are architectural, built into the system design from the start. Compliance controls are documented and available on request (security questionnaires for your audits).
- Ongoing phase (H1 2026): SOC 2 Type I certification preparation, covering organizational security audit, access controls, and incident management.
- Planned phase (H2 2026): ISO 27001, information security management system.
For clients with specific certification requirements today, SkaLean can provide: a third-party penetration test report (available on request under NDA), security architecture documentation, and a completed security questionnaire (SIG, CAIQ, or custom format). Specific compliance requirements of an Enterprise client are addressed from the discovery phase.
GDPR and Law 25 compliance is ensured at 5 levels in SkaLean.
- Data localization: option for processing exclusively on physical servers in Canada or your designated country. No transit to the US or other non-adequate countries without explicit agreement.
- Automatic PII detection and pseudonymization: 15 categories of personal data (names, emails, phones, insurance numbers, birthdates, medical data, financial data, etc.) are detected and pseudonymized before any LLM processing. Your company is the data controller; SkaLean acts as processor.
- Data subject rights: SkaLean provides tools to honor access, rectification, erasure (right to be forgotten), and portability requests. An individual can request deletion of all their data within 72 hours.
- Processing register: SkaLean automatically generates a GDPR-compliant processing register for your organization, including purposes, data categories, and subprocessors.
- DPA (Data Processing Agreement): a GDPR/Law 25-compliant data processing agreement is signed with each client, detailing SkaLean's obligations as processor.
When you ask SkaLean a question, an LLM inference occurs: a computing calculation that generates the response. Sovereign GPU hosting means this calculation happens on graphics processing units (GPUs) physically located in your country, operated by an entity subject to local laws.
Without GPU sovereignty, even if your data is stored in Canada, LLM computing is often delegated to US providers (AWS, Google Cloud, Azure, OpenAI) subject to the US Cloud Act of 2018, which compels these companies to provide data to US authorities on request, even if the data is physically outside the US.
Sectors that must use sovereign GPU:
- Sectors subject to HIPAA (medical clinics, hospitals)
- Sectors subject to OSFI (banks, insurance)
- Organizations subject to government regulations on citizen data protection
- Professions with strict professional secrecy obligations (lawyers, notaries)
Sovereign GPU is available on SkaLean Pro and Enterprise plans. With Starter plans using a cloud LLM, only relevant anonymized excerpts transit, never the complete document. For the sectors cited, we systematically recommend sovereign GPU.
SkaLean applies end-to-end encryption at two stages.
- In transit (moving data): all communications between your browser/app and SkaLean servers use TLS 1.3 (the most recent and secure version of the protocol). Communications between internal servers use mTLS (mutual TLS with authentication on both sides). No unencrypted HTTP communication is permitted in the infrastructure.
- At rest (stored data): all files (documents, vector base, logs) are encrypted with AES-256 (industry standard for sensitive data). Encryption keys are managed by a key management system (KMS) with automatic rotation every 90 days. For Enterprise clients, key management can be transferred to the client (BYOK: Bring Your Own Key), meaning SkaLean technically cannot access your data even in case of an external request.
Backups are also encrypted and stored in a separate region. Data retention after termination is 30 days by default (configurable from 7 to 90 days), then certified permanent deletion.
SkaLean has a documented 5-phase incident response plan.
- Detection: 24/7 continuous infrastructure monitoring with automatic alerts on abnormal behavior (unusual access, abnormal request volumes, intrusion attempts). Anomalies trigger an alert to the security team in under 5 minutes.
- Containment: immediate isolation of the affected area to stop spread, without cutting service for unaffected clients.
- Notification: in case of a confirmed breach involving personal data, SkaLean notifies affected clients within 24 hours (well within the 72 hours required by GDPR and the 30 days required by Law 25). You are then responsible for notification to your Data Protection Authority if required.
- Remediation: vulnerability fix, log analysis to determine incident scope, post-incident report delivered to client.
- Improvement: each incident undergoes a post-mortem with documented corrective actions. The report is shared with affected clients.
Availability SLA: 99% (Starter), 99.5% (Pro), 99.9% (Enterprise). Incident histories are published on the public status dashboard.
Yes. SkaLean has a standard compliance documentation package available to clients under NDA.
- Completed security questionnaire: SIG Lite format, CAIQ v4 (Cloud Security Alliance), or your organization's custom questionnaire. Includes technical, organizational, and physical controls.
- Documented security architecture: architecture diagrams with data flows, encryption points, network segmentation, and external access.
- Information security policy: 40+ page document covering access management, data classification, incident management, and business continuity.
- Penetration test report (pentest): conducted by an accredited third party, available under NDA. Frequency: annual and after any major architectural change.
- Risk analysis report: based on the ISO 27005 standard.
- Data Processing Agreement (DPA): GDPR/Law 25 compliant, customizable to your requirements.
For Enterprise clients, SkaLean can participate in your own security audits (custom questionnaires, security team interviews, architecture review). Standard turnaround for documentation: 5 business days.
Need a complete security dossier?
Our team prepares a personalized security dossier for your management and DPO. Architecture, compliance, encryption, logging: everything documented and verifiable.